The goal of this project was to develop a passive Google dork script to collect potentially vulnerable web pages and applications on the Internet. There are 2 parts. The first is
ghdb_scraper.py that retrieves Google Dorks and the second portion is pagodo.py that leverages the information gathered by ghdb_scraper.py.What are Google Dorks?
The awesome folks at Offensive Security maintain the Google Hacking Database (GHDB) found here: https://www.exploit-db.com/google-hacking-database. It is a collection of Google searches, called dorks, that can be used to find potentially vulnerable boxes or other juicy info that is picked up by Google's search bots.
Installation
Scripts are written for Python 3.6+. Clone the git repository and install the requirements.
git clone https://github.com/opsdisk/pagodo.git
cd pagodo
virtualenv -p python3 .venv # If using a virtual environment.
source .venv/bin/activate # If using a virtual environment.
pip install -r requirements.txtGoogle is blocking me!
If you start getting HTTP 503 errors, Google has rightfully detected you as a bot and will block your IP for a set period of time. The solution is to use proxychains and a bank of proxies to round robin the lookups.
Install proxychains4
apt install proxychains4 -y/etc/proxychains4.conf configuration file to round robin the look ups through different proxy servers. In the example below, 2 different dynamic socks proxies have been set up with different local listening ports (9050 and 9051). Don't know how to utilize SSH and dynamic socks proxies? Do yourself a favor and pick up a copy of The Cyber Plumber's Handbook to learn all about Secure Shell (SSH) tunneling, port redirection, and bending traffic like a boss.vim /etc/proxychains4.confround_robin
chain_len = 1
proxy_dns
remote_dns_subnet 224
tcp_read_time_out 15000
tcp_connect_time_out 8000
[ProxyList]
socks4 127.0.0.1 9050
socks4 127.0.0.1 9051proxychains4 in front of the Python script and each lookup will go through a different proxy (and thus source from a different IP). You could even tune down the -e delay time because you will be leveraging different proxy boxes.proxychains4 python3 pagodo.py -g ALL_dorks.txt -s -e 17.0 -l 700 -j 1.1ghdb_scraper.py
To start off,
pagodo.py needs a list of all the current Google dorks. A datetimestamped file with the Google dorks and the indididual dork category dorks are also provided in the repo. Fortunately, the entire database can be pulled back with 1 GET request using ghdb_scraper.py. You can dump all dorks to a file, the individual dork categories to separate dork files, or the entire json blob if you want more contextual data about the dork.To retrieve all dorks
python3 ghdb_scraper.py -j -spython3 ghdb_scraper.py -icategories = { 1: "Footholds", 2: "File Containing Usernames", 3: "Sensitives Directories", 4: "Web Server Detection", 5: "Vulnerable Files", 6: "Vulnerable Servers", 7: "Error Messages", 8: "File Containing Juicy Info", 9: "File Containing Passwords", 10: "Sensitive Online Shopping Info", 11: "Network or Vulnerability Data", 12: "Pages Containing Login Portals", 13: "Various Online devices", 14: "Advisories and Vulnerabilities", } pagodo.py
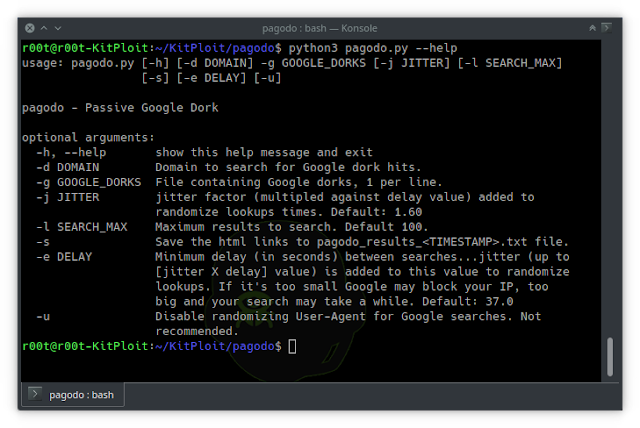
Now that a file with the most recent Google dorks exists, it can be fed into
pagodo.py using the -g switch to start collecting potentially vulnerable public applications. pagodo.py leverages the google python library to search Google for sites with the Google dork, such as:intitle:"ListMail Login" admin -demo -d switch can be used to specify a domain and functions as the Google search operator:site:example.com google module to allow for User-Agent randomization in the Google search queries. This feature is available in 1.9.3 and allows you to randomize the different user agents used for each search. This emulates the different browsers used in a large corporate environment.The second enhancement focuses on randomizing the time between search queries. A minimum delay is specified using the
-e option and a jitter factor is used to add time on to the minimum delay number. A list of 50 jitter times is created and one is randomly appended to the minimum delay time for each Google dork search.categories = {
1: "Footholds",
2: "File Containing Usernames",
3: "Sensitives Directories",
4: "Web Server Detection",
5: "Vulnerable Files",
6: "Vulnerable Servers",
7: "Error Messages",
8: "File Containing Juicy Info",
9: "File Containing Passwords",
10: "Sensitive Online Shopping Info",
11: "Network or Vulnerability Data",
12: "Pages Containing Login Portals",
13: "Various Online devices",
14: "Advisories and Vulnerabilities",
}intitle:"ListMail Login" admin -demoTo run it:
site:example.comConclusion
Comments, suggestions, and improvements are always welcome. Be sure to follow @opsdisk on Twitter for the latest updates.
via KitPloit
Read more
- Pentest Automation Tools
- Hacker Search Tools
- Hacking Tools Software
- Hacking Tools
- New Hack Tools
- Pentest Reporting Tools
- Hack Tool Apk
- Hacker Techniques Tools And Incident Handling
- Hack Website Online Tool
- Hack Tools Online
- Hacker Tools For Pc
- Hacker Tools
- Pentest Tools Windows
- Pentest Tools Kali Linux
- Hacker Security Tools
- Beginner Hacker Tools
- Hack Tool Apk No Root
- Game Hacking
- Physical Pentest Tools
- Pentest Box Tools Download
- Hacking Tools Pc
- Pentest Tools Url Fuzzer
- New Hack Tools
- Pentest Tools Open Source
- Hack Tools For Pc
- Game Hacking
- Pentest Box Tools Download
- Hackrf Tools
- Hacking Tools For Windows Free Download
- Hacking Tools
- Best Hacking Tools 2019
- Pentest Tools Review
- Top Pentest Tools
- Hacking Tools For Kali Linux
- Hacking Tools And Software
- Hacking Tools Download
- Nsa Hack Tools
- Hack Tools Github
- Install Pentest Tools Ubuntu
- Hacking Tools Pc
- Hack Tool Apk
- What Are Hacking Tools
- Tools Used For Hacking
- Hacking Tools For Windows
- Hack Tools Download
- Growth Hacker Tools
- Easy Hack Tools
- Hacking App
- Hacker Tools Apk
- Hacker Tools For Mac
- Wifi Hacker Tools For Windows
- Pentest Tools Review
- Hack Tools For Ubuntu
- Hack Apps
- Hacker Tools 2020
- Beginner Hacker Tools
- Pentest Reporting Tools
- Pentest Tools For Ubuntu
- Hacking Tools Kit
- Hack Tools For Windows
- Hacking Tools Software
- Hacks And Tools
- Hacking Tools For Kali Linux
- Hacker Tools Software
- Pentest Tools Tcp Port Scanner
- Kik Hack Tools
- Hacker Tools List
- Hack Tool Apk
- Nsa Hack Tools
- What Is Hacking Tools
- Pentest Tools Open Source
- How To Install Pentest Tools In Ubuntu
- Pentest Tools
- Hacker Tools Software
- Hacking Tools For Beginners
- Blackhat Hacker Tools
- New Hack Tools
- Pentest Tools Nmap
- Tools For Hacker
- Hacker Tools 2020
- Hacking Tools For Games
- Hack Tools Github
- Hacker Tool Kit
- Hack Tools Mac
- How To Install Pentest Tools In Ubuntu
- Tools 4 Hack
- Hacking Tools For Beginners
- Hacking App
- Hacking Tools Pc
- Pentest Tools Linux
- Pentest Tools Download
- Hacking Tools Name
- Hack Tools For Pc
- Hacking Tools Kit
- Hacking Tools Windows 10
- Hacking App
- What Are Hacking Tools
- How To Install Pentest Tools In Ubuntu
- What Is Hacking Tools
- Nsa Hacker Tools
- How To Install Pentest Tools In Ubuntu
- Hacking Tools Kit
- Pentest Tools Apk
- Hacking Tools Github
- How To Hack
- Hacking Tools Free Download
- Hacker Tools Github
- Tools For Hacker
- Bluetooth Hacking Tools Kali
- Hacking App
- Hacking Apps
- Hacker Tools 2020
- Hack Tool Apk
- Hacking Tools For Pc
- Hacker Tools Free
- Black Hat Hacker Tools
- New Hack Tools
- Top Pentest Tools
- Pentest Tools Bluekeep
- Pentest Tools Website
- Hacking Tools Download
- Top Pentest Tools
- Hack Tool Apk
- Pentest Tools Online
- Pentest Tools Online
- Hack Website Online Tool
- Hacking Tools Download
- Hacking Tools Kit
- Nsa Hack Tools Download
- Hacking Tools For Games
- Hacker Tools Hardware
- Hack Rom Tools
0 comments:
Post a Comment